🎧 Listen to this article
Prefer to listen? An audio version of this article is available for accessibility and convenience.
Every push notification on your iPhone leaves a digital paper trail. Apple stores metadata about which apps send you notifications, when they arrive, and which Apple ID receives them — and law enforcement can access that data with a court order. Since 2022, government requests for iPhone push notification records have grown more than fivefold, according to Apple’s own transparency reports.
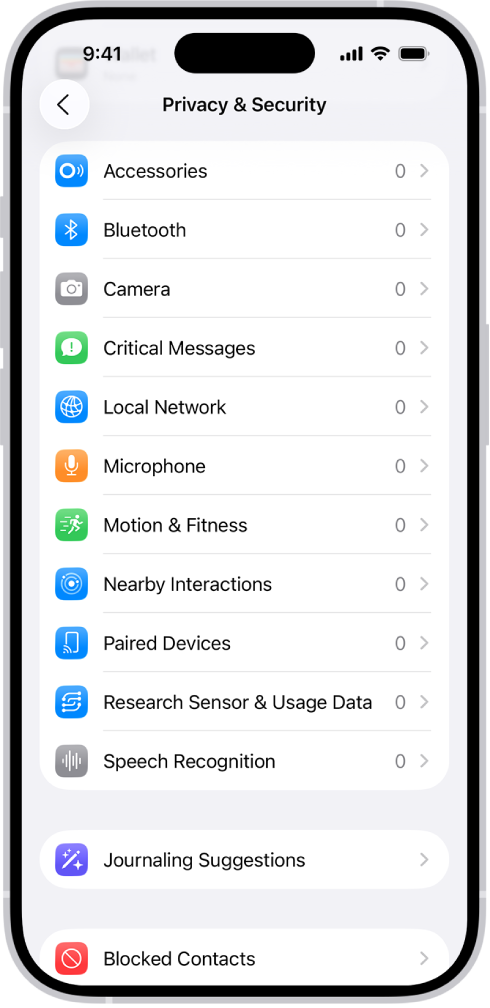
The settings controlling this exposure are scattered across at least three different menus in iOS 26. Most of them default to wide open. You are broadcasting more about your digital life through notification banners than you probably realize, and the handful of changes that actually reduce that exposure take about four minutes to configure.
 Ad
AdWhat Your Push Notifications Actually Expose
When an app sends you a notification, it does not travel directly from the developer to your iPhone. Every single one routes through Apple Push Notification service — APNs for short. Apple generates a unique push token that ties your device and that specific app to your Apple ID. Every notification that passes through their servers carries that token like a return address.
Apple knows which apps you have installed that send notifications. They know how often those apps ping you. They know the exact timestamps. And unless the developer encrypted the notification payload using a Notification Service Extension, the actual text content of each notification is readable on Apple’s servers.
Signal encrypts its push payloads. So does WhatsApp. Most other apps do not.
Apple publishes a push token transparency page that tracks law enforcement requests for this data. In the first half of 2025, Apple received 393 requests covering 966 individual push tokens. In the second half of 2022, that number was 70. The compliance rate has actually declined — Apple approved fewer requests proportionally in 2024 than in 2023 — but the raw volume keeps climbing. That trajectory should make every iPhone owner at least curious about what their notification settings actually do.
For a broader look at what iOS 26 changed for privacy, the iOS 26.4 settings guide covers more ground. What I want to focus on here is specifically the notification pipeline, because it is the one privacy surface most people never think about.
The Notification Database Nobody Mentions
This genuinely surprised me. Your iPhone keeps an internal notification database. Every notification that lands on your lock screen, Notification Center, or a Focus summary gets cached at the system level. iOS needs that database to display notification history, group alerts by app, and manage delivery priorities.
The catch? That cache persists even after you delete the app.
The FBI demonstrated this when they recovered deleted Signal messages from an iPhone — not from Signal’s own data, but from the iOS notification database that had stored the notification content when it originally arrived. This is not a bug or an exploit. It is standard iOS behavior. If a notification arrived with readable content — meaning the developer did not encrypt the payload — that text sits on your device in a system database most people would never know to look for.
 Ad
AdFive Settings That Shrink Your Notification Footprint in iOS 26
These settings will not eliminate the metadata trail entirely. Nothing short of disabling notifications completely will do that. But they meaningfully reduce what is visible on your device and what content is accessible if someone gains physical or legal access.
Show Previews: set it to Never. Open Settings, tap Notifications, then tap Show Previews at the top. Change it from Always to Never. By default, iOS displays notification content on your lock screen where anyone nearby can read it. “Never” means banners show the app name only — you authenticate with Face ID or your passcode to see the actual content. This is the single highest-impact privacy change for notifications, and the setting is buried two taps deeper than the main Notifications screen suggests. The label gives no hint that it controls lock screen visibility.
Disable notifications for sensitive apps entirely. Inside Settings, scroll to Notifications, find the specific app, and toggle Allow Notifications off. No notifications means no push tokens generated for that app on your device — no metadata trail through Apple’s servers. The tradeoff is real: you lose real-time alerts. For apps where content sensitivity matters more than immediacy, that tradeoff is worth making.
Turn on Advanced Data Protection for iCloud. Tap your name at the top of Settings, then iCloud, then Advanced Data Protection. This end-to-end encrypts most of your iCloud data including Notes, Messages backups, Photos, and Safari bookmarks. It does not encrypt push notification metadata — that runs through a separate system — but it closes an adjacent exposure point that compounds the risk.
Enable Stolen Device Protection. Settings, then Face ID & Passcode, scroll to Stolen Device Protection. This forces biometric authentication for sensitive changes when your iPhone is away from familiar locations. It will not change notification behavior directly, but it stops someone with your passcode from quietly disabling the protections that guard your notification data.
Choose apps that encrypt notification payloads. You have no toggle for this one. It depends entirely on whether the app developer built a Notification Service Extension to encrypt content before sending. Signal does. WhatsApp does. Your bank app probably does not. If notification content from a particular app would concern you in someone else’s hands, check whether your privacy settings cover it and consider turning off push notifications for that app and checking it manually instead.
Why Metadata Is the Exposure You Cannot Switch Off
Here is where I have to be straight with you. Even with every setting above locked down, Apple still sees the metadata. They know which apps notify your device. They know the timestamps. They know your push token and the Apple ID it maps to. That metadata is structural to how push notifications work — it cannot be encrypted because Apple’s servers need it to route each notification to the right device.
iOS 26 did make one meaningful improvement here. The notification priority system that sorts and ranks your alerts now runs entirely on-device. Your interaction data — which alerts you open, which you dismiss, what time you read them — stays on your iPhone and never leaves. Apple built the ranking model locally instead of phoning home, and that deserves genuine credit.
But the underlying architecture has not changed. Every app notification generates metadata on Apple’s infrastructure, and a court order unlocks it. Apple raised the legal bar in December 2023 by requiring a court order instead of a subpoena — a change they made only after Senator Ron Wyden publicly pointed out that Google already required one. Before that, law enforcement could request your push token data without any judicial review at all.
Push notifications are a privacy tradeoff baked into the architecture of every smartphone. You can shrink the surface — and after reading this, you should. Four minutes in your Settings app closes the widest gaps. The metadata will still flow, but what it reveals about you will be a lot less interesting.

Blaine Locklair
Founder of Zone of Mac with 25 years of web development experience. Every guide on the site is verified against Apple's current documentation, tested with real hardware, and written to be fully accessible to all readers.
follow me :

Related Posts
iOS 26.4 Dropped Ambient Music Widgets, and They’re Worth Setting Up
Apr 16, 2026
This iOS 26.4 Setting Lets Your iPhone Shazam Songs Offline
Apr 16, 2026
iPhone Live Activities: Every Setup Worth Trying in iOS 26
Apr 16, 2026